Cookies’ abilities have grown and evolved over the years, but they have left some legacy issues. To handle this, browsers (including Safari, Chrome, Firefox, and Edge) are changing their behavior regarding the SameSite and Secure attributes for a secure-by-default model for cookies.
As a 4D web developer, you may be concerned about the 4D web sessions session cookie if you want to prevent your application from Cross-site request forgery.
To prevent your web session cookie from circulating on the web pointlessly or being misunderstood by browsers because of a default value applied, you should ask if it is:
- a third-party cookie: associated with a domain name different from that of the page where the cookie is encountered. A third-party cookie is placed by a page object (e.g. an ad) originating from a domain other than the one hosting the page
or
- a first-party cookie: associated with the domain of the page
Depending on your use case, you should choose the appropriate value for the SameSite attribute of your web session cookie.
To reinforce security, the Secure attribute must be set for the web session cookie when the connection is secured (HTTPS) to indicate to the browser that the cookie can be sent safely.
Keep reading to learn how 4D has your back to improve privacy and security across the web.
To enable you to choose how your web server should behave, we have enhanced the web server object by adding a new sessionCookieSameSite property.
Set a Samesite attribute value
By default, the web server will set the SameSite attribute of the session cookie to “Strict“. We’ve chosen this value because it’s the safest.
If you want another value, use the WEB Server command:
var $webServer; $settings : Object
$settings:=New object()
$webServer:=WEB Server
$settings.sessionCookieSameSite:=Web SameSite Lax
$webServer.stop()
$webServer.start($settings)
Each sensitivity value for the SameSite attribute is provided in the 4D language with specific constants:
- Web SameSite Lax = “Lax”
- Web SameSite Strict = “Strict”
- Web SameSite None = “None”
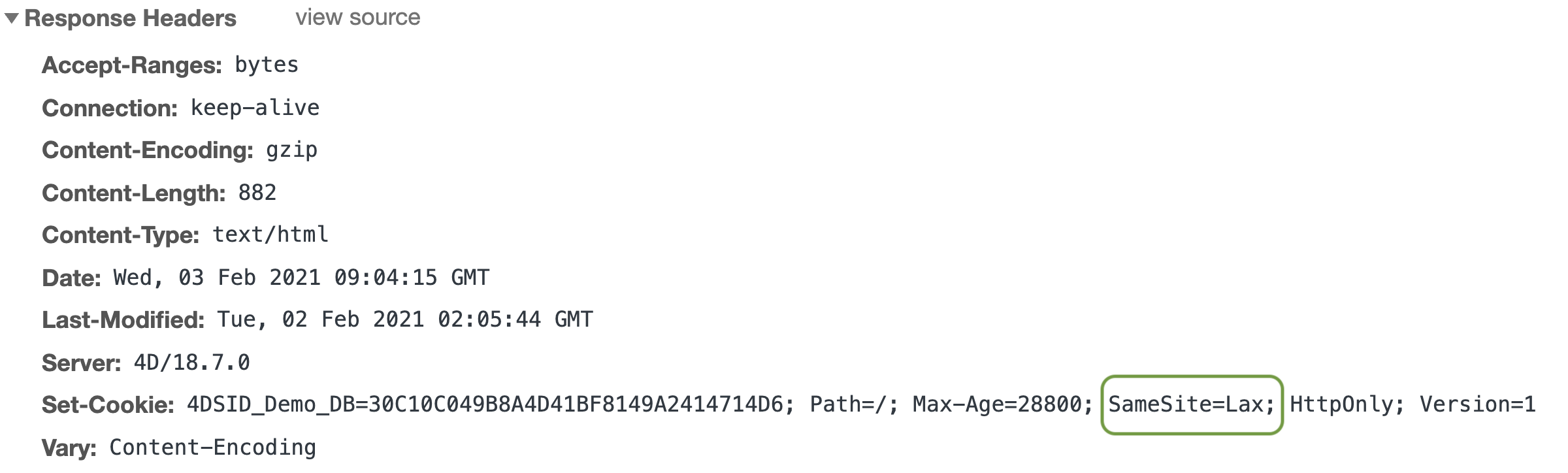
Here is an overview of what you’ll see in your browser:
and the secure attribute?
If the SameSite attribute value is “None”, some browsers may require the Secure attribute to be set to another value in order to send it (only if the connection is HTTPS).
The good news is that the 4D web server handles this automatically.
If a connection is HTTPS, the session cookie is automatically set with the Secure attribute, so that browsers will send it.
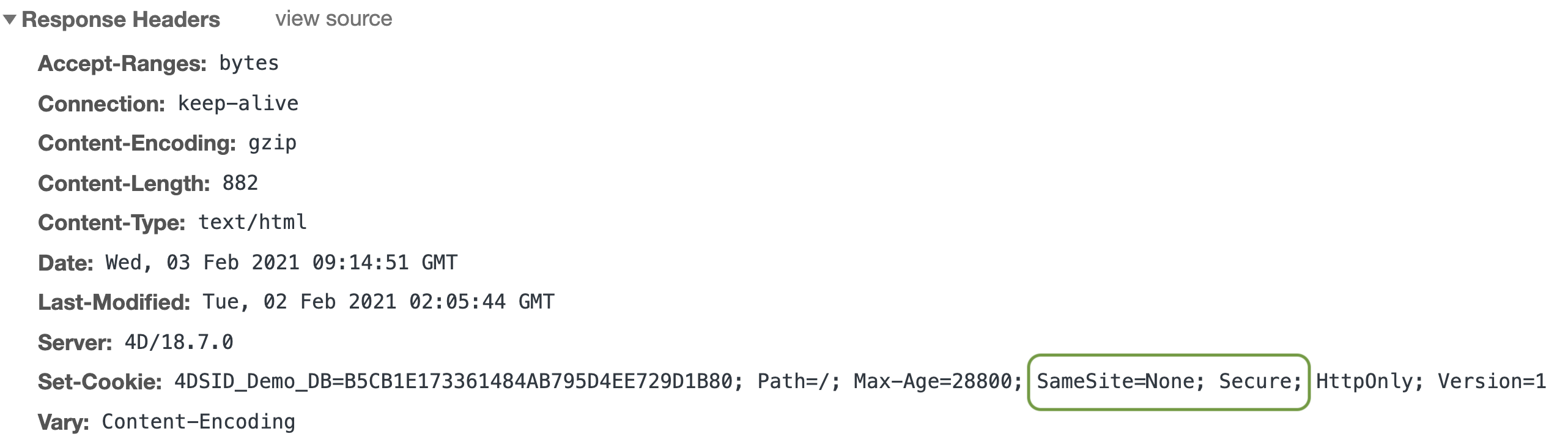
Here is an overview of what you’ll see in your browser with an HTTPS connection:
Now let’s work safely with our web applications and discuss this on the forum!

Comments are not currently available for this post.